GHSA-HM8R-95G3-5HJ9
Vulnerability from github – Published: 2024-03-25 19:45 – Updated: 2024-03-25 22:31Summary
An attacker with admin privileges can upload an attachment containing JS code without extension and the application will render it as HTML which allows for XSS attacks.
Details
When attachments are uploaded without an extension, the application renders it as HTML by default. Therefore allowing attackers to upload .html files containing javascript code to perform XSS attacks. The direct file path to the uploaded attachment is also easily obtainable as it is made up of substrings of the file's MD5 hashes.
PoC
-
Admin users can upload attachments containing XSS payloads in files without extensions to bypass the .html extension check.
-
Since the path of the uploaded file is built entirely on the file’s MD5 hash and the attachment directory, it is possible for an attacker to know the direct path of the uploaded file.
E.g file MD5 hash: 38fff51cb7248a06d6142c6bdf846831
URL will be: http://127.0.0.1/phpmyfaq/attachments/38fff/51cb7/248a0/6d6142c6bdf846831
- /attachments
- /38fff (first 5 chars of MD5 hash)
- /51cb7 (next 5 chars of MD5 hash)
- /248a0 (next 5 chars of MD5 hash)
- /6d6142c6bdf846831 (remaining chars of MD5 hash)
- Even though the attachment was uploaded without a file extension, it is still rendered as .html, hence triggering the XSS payload.
Impact
This allows an attacker to execute arbitrary client side JavaScript within the context of another user's phpMyFAQ session.
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "phpmyfaq/phpmyfaq"
},
"ranges": [
{
"events": [
{
"introduced": "3.2.5"
},
{
"fixed": "3.2.6"
}
],
"type": "ECOSYSTEM"
}
],
"versions": [
"3.2.5"
]
}
],
"aliases": [
"CVE-2024-29179"
],
"database_specific": {
"cwe_ids": [
"CWE-79"
],
"github_reviewed": true,
"github_reviewed_at": "2024-03-25T19:45:12Z",
"nvd_published_at": "2024-03-25T21:15:47Z",
"severity": "MODERATE"
},
"details": "### Summary\nAn attacker with admin privileges can upload an attachment containing JS code without extension and the application will render it as HTML which allows for XSS attacks.\n\n### Details\nWhen attachments are uploaded without an extension, the application renders it as HTML by default. Therefore allowing attackers to upload .html files containing javascript code to perform XSS attacks. The direct file path to the uploaded attachment is also easily obtainable as it is made up of substrings of the file\u0027s MD5 hashes.\n\n### PoC\n1. Admin users can upload attachments containing XSS payloads in files without extensions to bypass the .html extension check.\n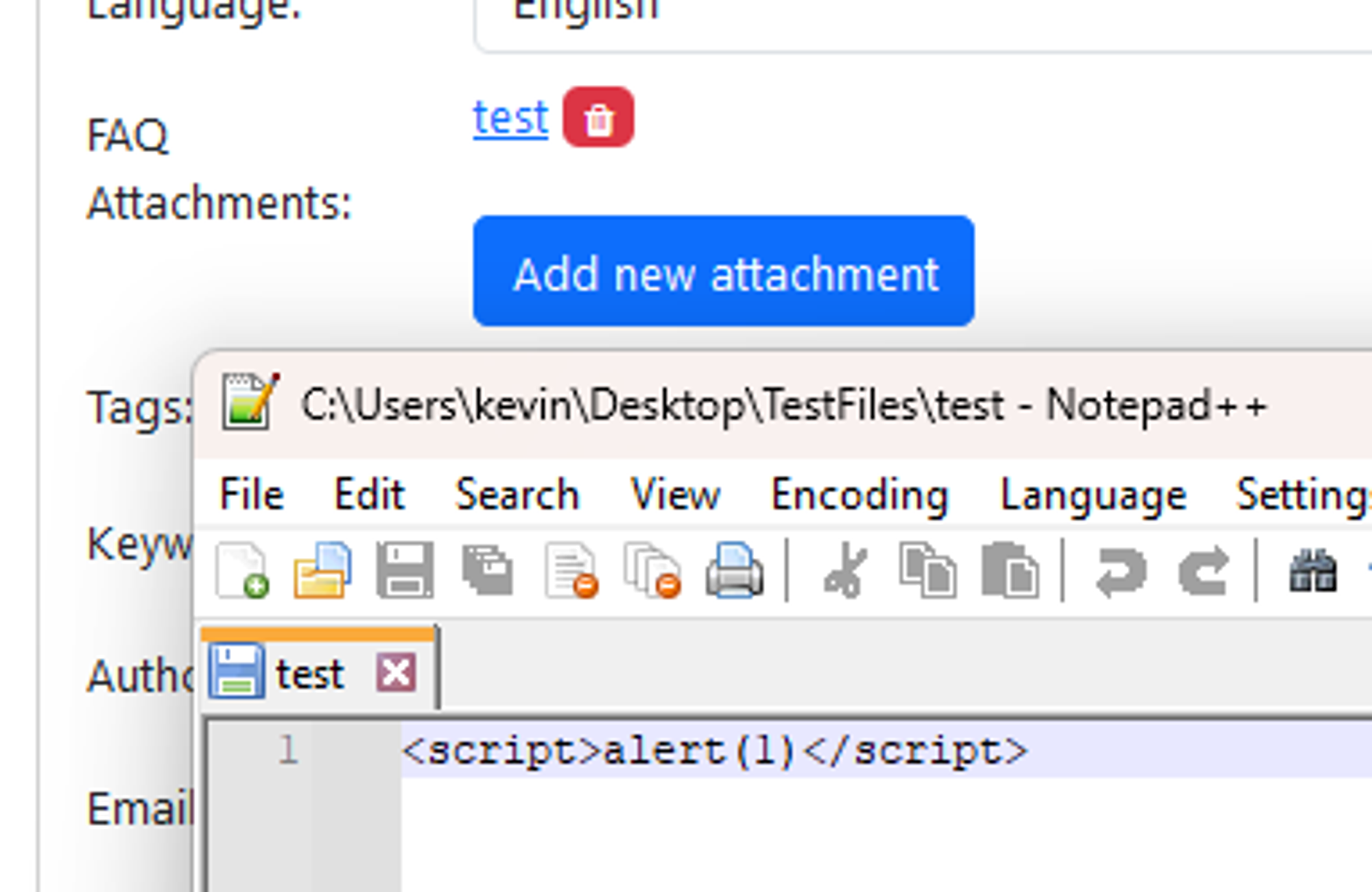\n\n2. Since the path of the uploaded file is built entirely on the file\u2019s MD5 hash and the attachment directory, it is possible for an attacker to know the direct path of the uploaded file.\n\n E.g file MD5 hash: 38fff51cb7248a06d6142c6bdf846831\n\n URL will be: http://127.0.0.1/phpmyfaq/attachments/38fff/51cb7/248a0/6d6142c6bdf846831\n\n - /attachments\n - /38fff (first 5 chars of MD5 hash)\n - /51cb7 (next 5 chars of MD5 hash)\n - /248a0 (next 5 chars of MD5 hash)\n - /6d6142c6bdf846831 (remaining chars of MD5 hash)\n\n3. Even though the attachment was uploaded without a file extension, it is still rendered as .html, hence triggering the XSS payload.\n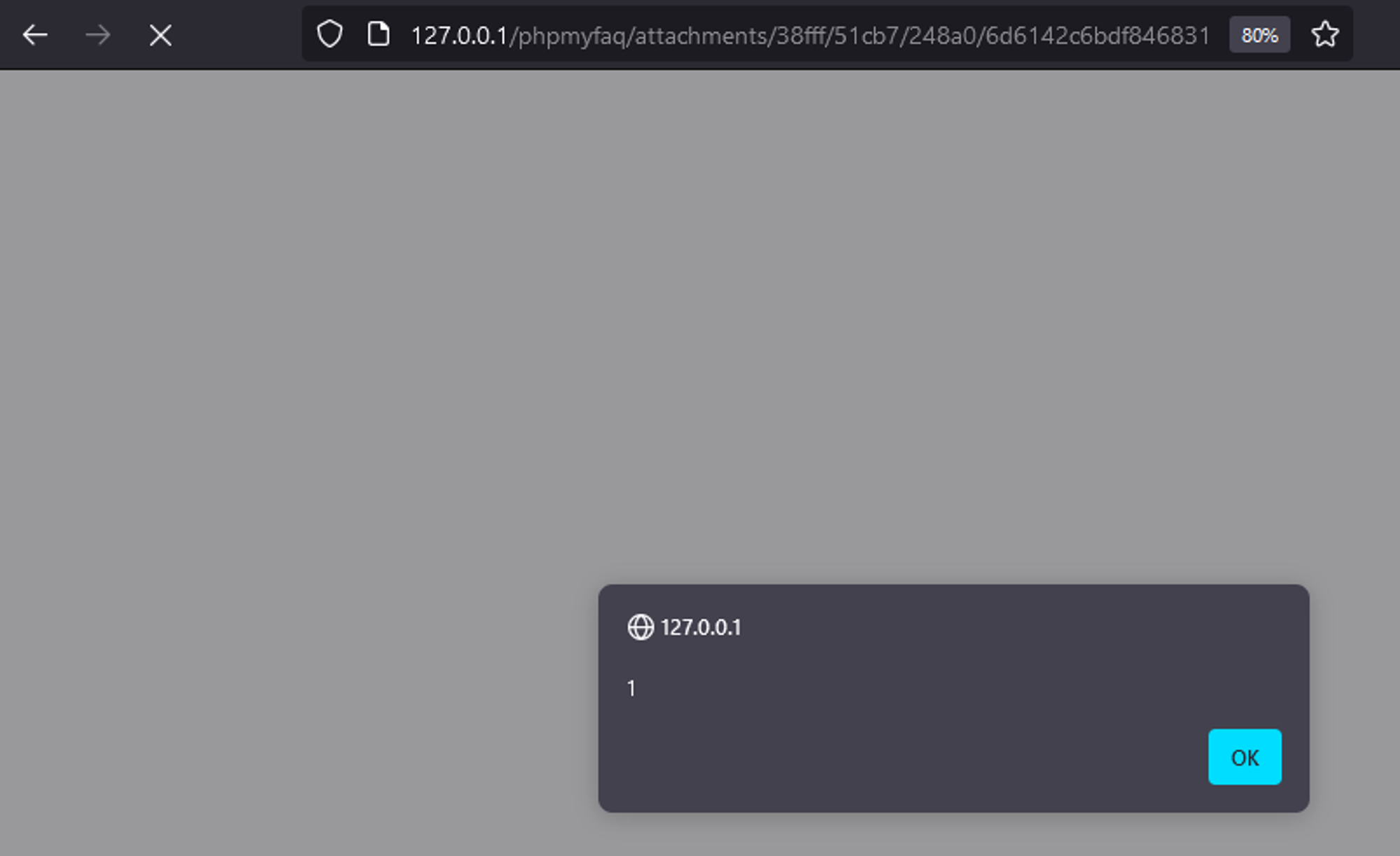\n\n### Impact\nThis allows an attacker to execute arbitrary client side JavaScript within the context of another user\u0027s phpMyFAQ session.\n\n",
"id": "GHSA-hm8r-95g3-5hj9",
"modified": "2024-03-25T22:31:44Z",
"published": "2024-03-25T19:45:12Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/thorsten/phpMyFAQ/security/advisories/GHSA-hm8r-95g3-5hj9"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-29179"
},
{
"type": "PACKAGE",
"url": "https://github.com/thorsten/phpMyFAQ"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:U/C:L/I:L/A:L",
"type": "CVSS_V3"
}
],
"summary": "phpMyFAQ Stored Cross-site Scripting at File Attachments"
}
Sightings
| Author | Source | Type | Date |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.