ghsa-cwx6-cx7x-4q34
Vulnerability from github
Published
2024-04-22 18:37
Modified
2024-04-23 14:15
Severity ?
Summary
LibreNMS vulnerable to SQL injection time-based leads to database extraction
Details
Summary
SQL injection vulnerability in POST /search/search=packages in LibreNMS 24.3.0 allows a user with global read privileges to execute SQL commands via the package parameter.
Details
There is a lack of hygiene of data coming from the user in line 83 of the file librenms/includes/html/pages/search/packages.inc.php
PoC
https://doc.clickup.com/9013166444/p/h/8ckm0bc-53/16811991bb5fff6
Impact
With this vulnerability, we can exploit a SQL injection time based vulnerability to extract all data from the database, such as administrator credentials
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "librenms/librenms"
},
"ranges": [
{
"events": [
{
"introduced": "0"
},
{
"fixed": "24.4.0"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2024-32461"
],
"database_specific": {
"cwe_ids": [
"CWE-89"
],
"github_reviewed": true,
"github_reviewed_at": "2024-04-22T18:37:21Z",
"nvd_published_at": "2024-04-22T22:15:07Z",
"severity": "HIGH"
},
"details": "### Summary\nSQL injection vulnerability in POST /search/search=packages in LibreNMS 24.3.0 allows a user with global read privileges to execute SQL commands via the package parameter. \n\n### Details\nThere is a lack of hygiene of data coming from the user in line 83 of the file librenms/includes/html/pages/search/packages.inc.php\n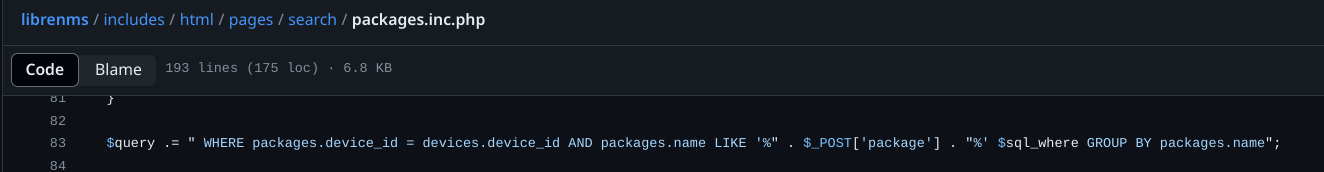\n\n### PoC\nhttps://doc.clickup.com/9013166444/p/h/8ckm0bc-53/16811991bb5fff6\n\n### Impact\nWith this vulnerability, we can exploit a SQL injection time based vulnerability to extract all data from the database, such as administrator credentials\n",
"id": "GHSA-cwx6-cx7x-4q34",
"modified": "2024-04-23T14:15:04Z",
"published": "2024-04-22T18:37:21Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/librenms/librenms/security/advisories/GHSA-cwx6-cx7x-4q34"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-32461"
},
{
"type": "WEB",
"url": "https://github.com/librenms/librenms/commit/d29201fce134347f891102699fbde7070debee33"
},
{
"type": "WEB",
"url": "https://doc.clickup.com/9013166444/p/h/8ckm0bc-53/16811991bb5fff6"
},
{
"type": "PACKAGE",
"url": "https://github.com/librenms/librenms"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"type": "CVSS_V3"
}
],
"summary": "LibreNMS vulnerable to SQL injection time-based leads to database extraction"
}
Loading…
Loading…
Sightings
| Author | Source | Type | Date |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or seen somewhere by the user.
- Confirmed: The vulnerability is confirmed from an analyst perspective.
- Exploited: This vulnerability was exploited and seen by the user reporting the sighting.
- Patched: This vulnerability was successfully patched by the user reporting the sighting.
- Not exploited: This vulnerability was not exploited or seen by the user reporting the sighting.
- Not confirmed: The user expresses doubt about the veracity of the vulnerability.
- Not patched: This vulnerability was not successfully patched by the user reporting the sighting.